Two-Factor Authentication
If you specify that a service uses two-factor authentication, then users must provide a second security token in addition to the first. With Caché 2015.2 there are two options for the second security token:
-
The system generates a pass code and sends it by text message to the user's mobile device. The user has a set amount of time to enter this code in order to gain access to the system. This requires that Caché have access to the user's mobile number. This approach has been available since Caché 2010.2.
-
Both Caché and an independent device controlled by the user generate a one time pass code using a Time-based One-time Password Algorithm (TOTP). The code generated by the user must match the code generated by Caché. This approach requires that both Caché and the user share a single secret key ahead of time and that the clocks on both the user's device and the Caché system are at least roughly synchronized. This approach is newly available in Caché 2015.2.
Here is the outline of the process for configuring the first of the above two-factor authentication approaches. See the note below for the location of more detail in the Caché documentation.
-
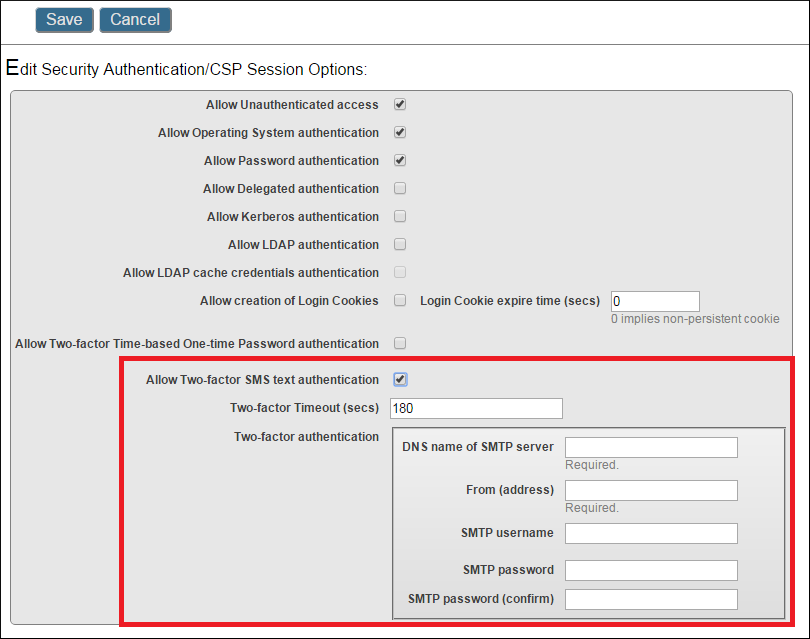
Enable and configure two-factor authentication system-wide. This involves first enabling the feature and then providing the details for the SMTP server that the Caché instance can use to send the message. You can do this on the Managment Portal's Edit Security Authentication/CSP Session Options page (click [Home] > [System Administration] > [Security] > [System Security] > [Authentication/CSP Session Options]).
-
If necessary, configure the mobile phone service provider. This involves creating an entry for the provider in the Portal. Click [Home] > [System Administration] > [Security] > [Mobile Phone] and enter the address for the provider's server for dispatching SMS messages. Note that many providers are predefined in the portal.
-
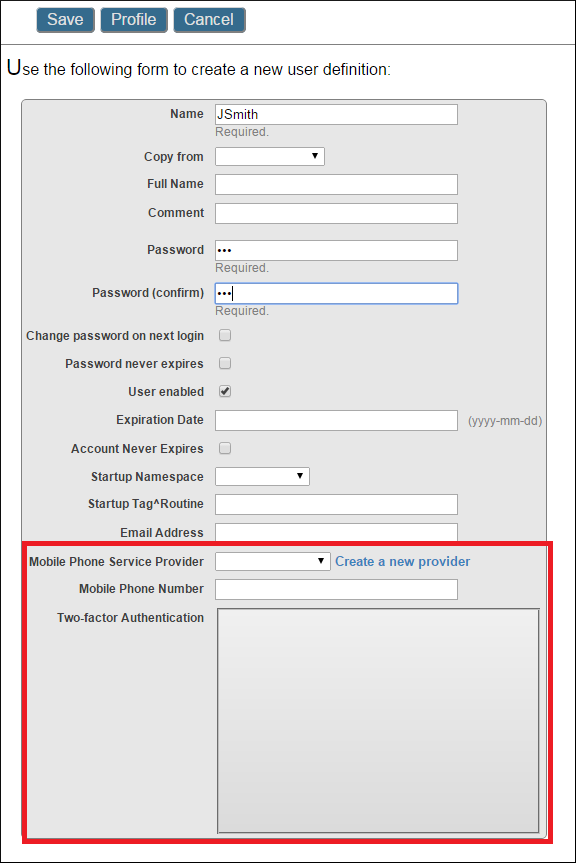
Configure users for two-factor authentication. This involves either updating the user's profile to include their mobile phone number and their service provider, or identifying the secret key to share with the user to use in the TOTP app. In the diagram below the Two-factor Authentication box would contain the secret key if this approach to two-factor authentication were enabled.
-
Enable two-factor security for the services that are going to use it. Note that once it is enabled for a service, it becomes required for all of a service's users.
For more details on configuring two-factor authentication, please read Configuring Two-factor Authentication in the Authentication section of the Caché Security Administration guide.