Controlling Access to Management Portal Functions
This appendix describes how the Management Portal uses the predefined security roles and resources to control access to Ensemble pages and options. It contains the following sections:
The Ensemble upgrade procedures reset these predefined resources and roles; therefore, you should customize security only by configuring resources and roles that you create yourself.
Introduction
In addition to the basic Caché roles, Ensemble contains predefined roles which you can use to control access to the functions in the Management Portal. While these built-in roles may suit most environments, you can add additional roles to customize access to pages or functions.
The following sections describe the security structure prebuilt in Ensemble. You can use this information to determine how to assign your users to roles in your environment:
For an in-depth description of Caché security, see the Caché Security Administration Guide, in particular, “Authorization: Controlling User Access” in the chapter “About Caché Security.”
Predefined Ensemble Resources
This section describes the Ensemble predefined resources, which all begin with the %Ens_ prefix.
-
The first subsection lists resources that protect a specific activity you can perform in Ensemble.
-
The second subsection lists Ensemble code and data resources.
You can view the list of predefined Ensemble resources on the Resources page of the Management Portal (select System Administration > Security > Resources from the Home page).
For an in-depth discussion of resources, see “Assets and Resources” in the Caché Security Administration Guide.
Ensemble Resources to Protect Activities
| Resource | Description |
|---|---|
| %Ens_ConfigItemRun | Controls starting and stopping configuration items |
| %Ens_DTLTest | Grants access to the data transformation testing utility |
| %Ens_Dashboard | Grants access to the Ensemble Production Monitor |
| %Ens_Deploy | Grants access to deployment activities |
| %Ens_DeploymentPkg | Controls the creation of deployment packages |
| %Ens_EventLog | Grants access to the Event Log |
| %Ens_MessageContent | Grants access to the contents of messages |
| %Ens_MessageDiscard | Controls discarding of queued and suspended messages |
| %Ens_MessageEditResend | Grants access to edit and resend messages |
| %Ens_MessageHeader | Grants access to message header data |
| %Ens_MessageResend | Grants access to resend messages |
| %Ens_MessageResubmit | Controls resubmission of suspended messages |
| %Ens_MessageSuspend | Controls the manual suspension of messages |
| %Ens_MessageTrace | Grants access to message trace |
| %Ens_MsgBank_Dashboard | Grants access to the Enterprise Monitor Page |
| %Ens_MsgBank_EventLog | Grants access to the Message Bank Event Log |
| %Ens_MsgBank_MessageContent | Grants access to the contents of messages in the Message Bank |
| %Ens_MsgBank_MessageEditResend | Grants permission to edit and resend messages from the Message Bank |
| %Ens_MsgBank_MessageHeader | Grants access to Message Bank header data |
| %Ens_MsgBank_MessageResend | Grants permission to resend messages from the Message Bank |
| %Ens_MsgBank_MessageTrace | Grants access to the Message Bank Visual Trace |
| %Ens_Portal* | Grants access to the Ensemble menus in the Management Portal |
| %Ens_ProductionDocumentation | Controls the creation of production documentation |
| %Ens_ProductionRun | Controls starting and stopping productions |
| %Ens_Purge | Controls purging of Ensemble data |
| %Ens_RuleLog | Grants access to the rule log |
| %Ens_TestingService | Grants access to the business host testing service |
| %Ens_ViewFileSystem | Grants access to the Finder Dialog which allows the user to view the file system |
* In addition to the %Ens_Portal resource, access to Ensemble functions in the Management Portal in any given namespace requires the Read permission on the default global database resource for that namespace. This check is enforced for access to all Ensemble portal pages.
Ensemble Resources to Protect Code and Data
| Resource | Code/Data |
|---|---|
| %Ens._AlertAdministration | Grants access to managed alert administration. |
| %Ens_Alerts | Grants access to alert configuration and management |
| %Ens_ArchiveManager | Grants access to the Archive Manager |
| %Ens_BPL | Grants access to BPL |
| %Ens_BusinessRules | Grants access to business rules |
| %Ens_Code | Grants access to all Ensemble classes and routines |
| %Ens_Credentials | Grants access to Ensemble credentials |
| %Ens_DTL | Grants access to DTL |
| %Ens_EDISchema | Grants access to EDI schemas |
| %Ens_EDISchemaAnnotation | Grants access to the HL7 Annotation classes. |
| %Ens_Jobs | Grants access to job data |
| %Ens_LookupTables | Grants access to lookup tables |
| %Ens_MsgBank | Grants access to Message Bank status information |
| %Ens_MsgBankConfig | Grants access to Message Bank configuration |
| %Ens_ProductionConfig | Grants access to production configuration activities |
| %Ens_PurgeSchedule | Grants access to scheduling of Ensemble purge tasks |
| %Ens_Queues | Grants access to queue data |
| %Ens_RecordMap | Grants access to Ensemble record maps |
| %Ens_RoutingRules | Grants access to routing rules |
| %Ens_Rules | Grants access to all Ensemble rules |
| %Ens_SequenceManager | Grants access to the Sequence Manager |
| %Ens_SystemDefaultConfig | Grants access to system default settings |
| %Ens_WorkflowConfig | Grants access to workflow roles and users |
In many cases, Ensemble default behavior uses a less granular resource (like %Ens_Code) which protects multiple data sources including the data protected by a more specific resource (like %Ens_BPL). The predefined Ensemble roles and privileges use the less granular resource, but you can choose alternative roles with more selective privileges.
Predefined Ensemble Roles
Ensemble also contains a set of predefined roles, each beginning with the %EnsRole_ prefix. These are roles designed to reasonably secure your Ensemble instances in both development and production environments. The following descriptions contain an overview of the perceived job responsibilities of members of the role and how these roles relate to other Ensemble roles.
Role for a trusted and skilled Ensemble administrator. In a live or test system this is for the person able to stop, start, and configure productions; to stop and start individual configuration items; to look at all logs, messages, and queues; to purge data; to add Ensemble default system settings; and so on. This administrator has almost unlimited ability to control the Ensemble environment, but cannot change code components other than to deploy updates.
This role is intentionally distinct from Caché administrative roles and does not grant the user any Caché-level privileges.
The %EnsRole_Administrator role is a member of the %EnsRole_Operator role, and, therefore, also holds all the privileges of that role.
Role for a person developing business logic, data structures, or core Ensemble code. This includes writing code in Studio, writing DTL and BPL in either Studio or using the web interface, developing routing rules, and creating custom message schemas (HL7, record mapping, XML, etc). In addition, this role allows a user to perform many administrative tasks, as the developer should have the ability to actively debug and test various options on development instances.
By default, members of the Ensemble developer role have full programming power and as such, can modify DTL, BPL, and record maps. Ensemble provides separate resources for each type of code if you want to distinguish areas of development by creating custom roles.
The %EnsRole_Developer role is a member of both the %Developer and %EnsRole_WebDeveloper roles. Therefore, a user assigned to this role can perform all Caché development tasks as well as the Ensemble web developer tasks.
Role for a person with limited development abilities. In particular, this restricts a user to the development tasks in the Ensemble menus of the Management Portal, like BPL, DTL, defining rules, and creating record maps. The role does not grant access to Studio or the terminal.
This role is a member of the %EnsRole_RulesDeveloper and %EnsRole_Operator role, so that a user that is a member of this role can perform debugging tasks in the Management Portal.
Role for a business analyst allowed to modify business rules dynamically. If you have developed a business process that requires such a function, you can allow a small number of people to modify the rules. This is not an administrative or development function.
%EnsRole_WebDeveloper is a member of this role.
Role for a generic user to view the Ensemble system monitor and the production monitor. Actions that would leave an audit trail if done from a user with %EnsRole_Operator have no effective audit trail from this generic username and therefore access needs to be restricted to a subset that does not include any risk of seeing sensitive data.
Role for operation staff managing the day-to-day status of a particular production. Users assigned to this role have the Read permission on the current configuration to determine what settings and code are in effect, but do not have permissions to modify the configuration. Operations staff may start and stop interfaces, and may start and stop the production. They do not have access to the contents of messages, but may resend messages which cause issues. Operators may view queue and job information, and may inspect the settings for purges, alerts, credentials, and lookup tables.
Both %EnsRole_Administrator and %EnsRole_WebDeveloper are members of this role.
Role for processing managed alerts assigned to any user or unassigned. For more information on processing managed alerts, see “Acting on Alerts by Viewing My Managed Alerts”.
Role for processing managed alerts assigned to current user or unassigned. For more information on processing managed alerts, see “Acting on Alerts by Viewing My Managed Alerts”.
Role that allows user to control the subscription criteria used to select messages and to specify the users to receive the messages. This role provides access to the management portal page that controls Publish and Subscribe routing. For more information on Publish and Subscribe messages, see “Defining Publish and Subscribe Message Routing”.
The default Ensemble security framework assigns permissions to the predefined resources, thus creating privileges for each of these roles. You can choose to assign the users of your application to these Ensemble roles or create your own roles, assigning them permissions to the Ensemble resources. If you upgrade your Ensemble instance, the procedures reset the default Ensemble roles, so you should make your configuration modifications only on user-created roles.
The next section shows the privileges assigned by default to each role.
You can view the list of predefined Ensemble roles on the Roles page of the Management Portal (select System Administration > Security > Roles from the Home page).
These roles only cover functions in the Ensemble menus of the Management Portal. Users in your environment likely require additional Caché roles. For details, see “Roles” in the Caché Security Administration Guide.
Default Privileges of the Predefined Ensemble Roles
This section lists the default privileges that each Ensemble role has for each Ensemble resource.
-
The first subsection lists the role privileges for the activity resources.
-
The second subsection lists the role privileges for the code and data resources.
See “Privileges and Permissions” in the Caché Security Administration Guide for an explanation of how you grant access to resources through role privileges.
Role Privileges for the Activity Resources
The following table lists the role privileges for the activity resources. Only the Use permission is required for access, use this permission on the underlying resource to determine access to data as well.
| Resource | %EnsRole _Administrator | %EnsRole _Developer* | %EnsRole _Monitor | %EnsRole _Operator |
|---|---|---|---|---|
| %Ens_ConfigItemRun | Use | Use | Use | |
| %Ens_DTLTest | Use | Use | ||
| %Ens_Dashboard | Use | Use | Use | Use |
| %Ens_Deploy | Use | |||
| %Ens_DeploymentPkg | Use | Use | ||
| %Ens_EventLog | Use | Use | Use | |
| %Ens_MessageContent | Use | Use | ||
| %Ens_MessageDiscard | Use | Use | ||
| %Ens_MessageEditResend | Use | Use | ||
| %Ens_MessageHeader | Use | Use | Use | |
| %Ens_MessageResend | Use | Use | Use | |
| %Ens_MessageResubmit | Use | Use | ||
| %Ens_MessageSuspend | Use | Use | ||
| %Ens_MessageTrace | Use | Use | Use | |
| %Ens_MsgBank_Dashboard | Use | Use | Use | Use |
| %Ens_MsgBank_EventLog | Use | Use | Use | |
| %Ens_MsgBank_MessageContent | Use | Use | ||
| %Ens_MsgBank_MessageEditResend | Use | Use | ||
| %Ens_MsgBank_MessageHeader | Use | Use | Use | |
| %Ens_MsgBank_MessageResend | Use | Use | Use | |
| %Ens_MsgBank_MessageTrace | Use | Use | Use | |
| %Ens_Portal* | Use | Use | Use | Use |
| %Ens_ProductionDocumentation | Use | Use | ||
| %Ens_ProductionRun | Use | Use | Use | |
| %Ens_Purge | Use | Use | ||
| %Ens_RuleLog* | Use | Use | Use | |
| %Ens_TestingService | Use | Use | ||
| %Ens_ViewFileSystem | Use | Use |
Role Privileges for the Code and Data Resources
The following table lists the role privileges for the code and data resources. Read and Write permissions are distinct for the resource; your application code should use these two permissions to determine access to the underlying data.
For reasons of space, this table does not include the information on all roles. Additional roles are described after the table.
| Resource | %EnsRole _Administrator | %EnsRole _Developer | %EnsRole _Monitor | %EnsRole _Operator |
|---|---|---|---|---|
| %Ens_Alerts | Read, Write | Read, Write | Read | |
| %Ens_ArchiveManager | Read, Write | |||
| %Ens_BPL | ||||
| %Ens_BusinessRules | ||||
| %Ens_Code | Read | Read, Write | ||
| %Ens_Credentials | Read, Write | Read | Read | |
| %Ens_DTL | ||||
| %Ens_EDISchema | Read | Read, Write | ||
| %Ens_Jobs | Read, Write | Read, Write | Read | |
| %Ens_LookupTables | Read, Write | Read, Write | Read | |
| %Ens_MsgBank | Read, Write | Read | Read | |
| %Ens_MsgBankConfig | Read, Write | Read, Write | ||
| %Ens_ProductionConfig | Read, Write | Read, Write | Read | |
| %Ens_PurgeSchedule | Read, Write | Read | Read | |
| %Ens_Queues | Read, Write | Read, Write | Read | |
| %Ens_RecordMap | ||||
| %Ens_RoutingRules | ||||
| %Ens_Rules* | Read, Write | |||
| %Ens_SequenceManager | Read, Write | Read, Write | ||
| %Ens_SystemDefaultConfig | Read, Write | Read | Read | |
| %Ens_WorkflowConfig | Write | Read, Write | Read |
Additional roles have the following privileges
-
The %EnsRole_WebDeveloper role has the same privileges as %EnsRole_Developer.
-
The %EnsRole_RulesDeveloper role has only the following privileges:
-
%Ens_Portal:U
-
%Ens_RuleLog:U
-
%Ens_Rules:RW
-
Portal Page Privilege Requirements
Each Management Portal page has a default privilege requirement in the security framework shipped with Ensemble. You can view this requirement while in the columns view of the portal menu just beneath where you click Go to navigate to the page. You only see this information if you click next to the menu item name and not directly on the label.
For example, when you click to the right of Production on the Ensemble Configure menu of the Management Portal, you see %Ens_ProductionConfig:READ listed under the System Resource(s) label. This means you must be a member of a role that has the Read permission on the %Ens_ProductionConfig resource to view the Production Configuration page.
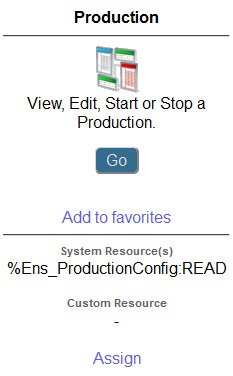
Notice you may also assign custom resources to a portal page. See “Using Custom Resources with the Management Portal” in the chapter “Assets and Resources” in the Caché Security Administration Guide.
Default SQL Privileges of the Predefined Ensemble Roles
Several Ensemble pages in the Management Portal use SQL queries to retrieve information; therefore, Ensemble users must have privileges on the appropriate tables to view this information. This section shows how Ensemble assigns SELECT privileges to its predefined roles to provide the proper security.
The %EnsRole_Administrator, %EnsRole_Developer, and %EnsRole_WebDeveloper roles hold the SELECT privilege on all of the following Ensemble SQL tables:
-
Ens.BusinessProcess
-
Ens.BusinessProcessBPL
-
Ens.MessageBody
-
Ens.MessageHeader
-
Ens.StreamContainer
-
Ens.StringContainer
-
EnsLib_DICOM.Document
-
EnsLib_EDI_ASTM.Document
-
EnsLib_EDI_ASTM.SearchTable
-
EnsLib_EDI_EDIFACT.Document
-
EnsLib_EDI_EDIFACT.SearchTable
-
EnsLib_EDI_X12.Document
-
EnsLib_EDI_X12.SearchTable
-
EnsLib_EDI_XML.Document
-
EnsLib_EDI.XML.SearchTable
-
EnsLib_HL7.Message
-
EnsLib_HL7.SearchTable
-
EnsLib_Printing.PrintJob
-
EnsLib_Printing.PrintRequest
-
EnsLib_SQL.Snapshot
-
EnsLib_XML.SearchTable
-
EnsLib_ebXML.Message
-
EnsLib_ebXML.MessageTracking
-
EnsLib_ebXML.MessageWithPayload
-
Ens_Config.Credentials
-
Ens_Enterprise_MsgBank.Log
-
Ens_Enterprise_MsgBank.MessageHeader
-
Ens_Enterprise_MsgBank.Node
-
Ens_Rule.Log
-
Ens_Rule.RuleLog
-
Ens_Util.Calendar
-
Ens_Util.IOLog
-
Ens_Util.Log
-
Ens_Util.Schedule
The remaining Ensemble roles have SELECT privileges on a subset of the Ensemble SQL tables as shown in the following table.
| SQL Table Name | %EnsRole _RulesDeveloper | %EnsRole _Monitor | %EnsRole _Operator |
|---|---|---|---|
| Ens.BusinessProcess | SELECT | ||
| Ens.BusinessProcessBPL | SELECT | ||
| Ens.MessageHeader | SELECT | ||
| Ens_Config.Credentials | SELECT | ||
| Ens_Enterprise_MsgBank.Log | SELECT | ||
| Ens_Enterprise_MsgBank.MessageHeader | SELECT | ||
| Ens_Enterprise_MsgBank.Node | SELECT | ||
| Ens_Rule.Log | SELECT | SELECT | |
| Ens_Rule.RuleLog | SELECT | SELECT | |
| Ens_Util.Calendar | SELECT | ||
| Ens_Util.Log | SELECT | SELECT | |
| Ens_Util.Schedule | SELECT |
Ensemble also grants EXECUTE privileges on the Ens.IsASub stored procedure (used in certain searches of the Message Viewer) to %EnsRole_Administrator, %EnsRole_Developer, and %EnsRole_WebDeveloper. If you define a custom role and want a user with the role to be able to perform searches on messages, you should grant this privilege to the role or user. To see if a specific role has this privilege in an Ensemble namespace:
-
Select System Administration, Security, and Roles.
-
Select the role.
-
Select the SQL Procedures tab.
-
Select the namespace from the drop-down menu.
If the role has the Ens.IsASub privilege, Ens.IsASub is listed and marked as having EXECUTE privilege. If the role does not have this privilege in the namespace, you can give it this privilege by doing the following on the SQL Procedures tab:
-
Click the Add Procedures ... button.
-
Select the Ens schema from the drop-down menu.
-
Select IsASub from the Available column.
-
Click the right arrow to add IsASub to the Selected column.
-
Click Apply and then Close.
You can also give this SQL procedure privilege directly to a user.
Ensemble automatically grants permissions to allow the specified roles to run SELECT statements as described in the previous tables. It grants these permissions for the tables generated for the built-in message types. If you define custom message types, you should grant the same permissions to these roles for the tables generated for these custom message types.
Customizing Ensemble Security
For information on customizing Ensemble security, see the following sections in Caché Security Administration Guide:
-
“Using Custom Resources with the Management Portal” in the chapter “Assets and Resources”
-
“Creating and Editing Users” in the chapter “Users”
-
“Web Applications” in the chapter “Applications”